What’s best for each MSP isn’t always the same.
Petra Security is the tool of choice for fast-growing MSPs who want best-in-class ITDR, and don’t need it bundled with their EDR, SAT, or other tools.
Petra is built for MSPs who prioritize Microsoft 365 protection.
Most security platforms treat Microsoft 365 as one module inside a broader stack. Detection is bundled with EDR, SAT, or general-purpose tooling. That approach provides coverage but not depth.
Petra takes a different approach:
Petra takes a different approach:
We focus exclusively on Microsoft 365 detection and response.
No bundling. No split attention. No diluted roadmap.
That focus enables deeper log ingestion and faster detection.
No bundling. No split attention. No diluted roadmap.
We monitor the parts attackers actually abuse.
No bundling. No split attention. No diluted roadmap.
We believe that M365 protection is worth investing in, because:
01
90% of today’s attacks are caused by phishing.
02
Most MSPs overwhelmingly face M365 attacks.
03
MFA bypass attacks are up 141% year-over-year.
04
BEC is now the #1 way businesses lose money to cybercrime.
The choice of Petra Security v. Huntress ITDR isn't really a question of 'which is better', it's a question of 'best-in-class' vs. 'bundled'.
We believe that if there's any protection worth investing in, it's this one. Petra is the choice for folks who want to make that investment.
We believe that if there's any protection worth investing in, it's this one. Petra is the choice for folks who want to make that investment.

We unlocked $500k in ARR and only expect these contracts to grow. I'd recommend any founders to go with Delve...I can't imagine how companies are getting compliant without Delve.

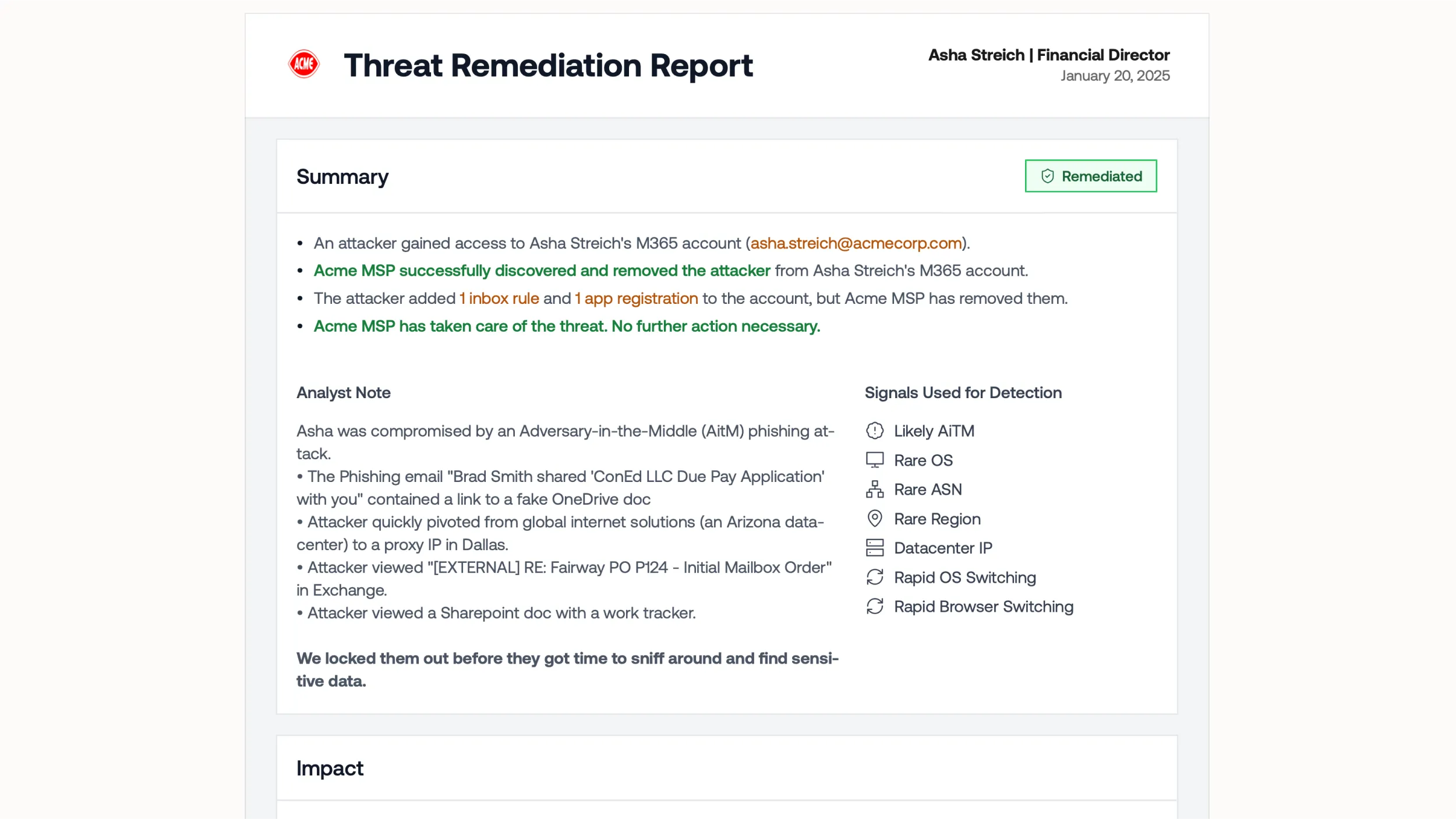
Detection Coverage
We focus exclusively on Microsoft 365 detection and response.
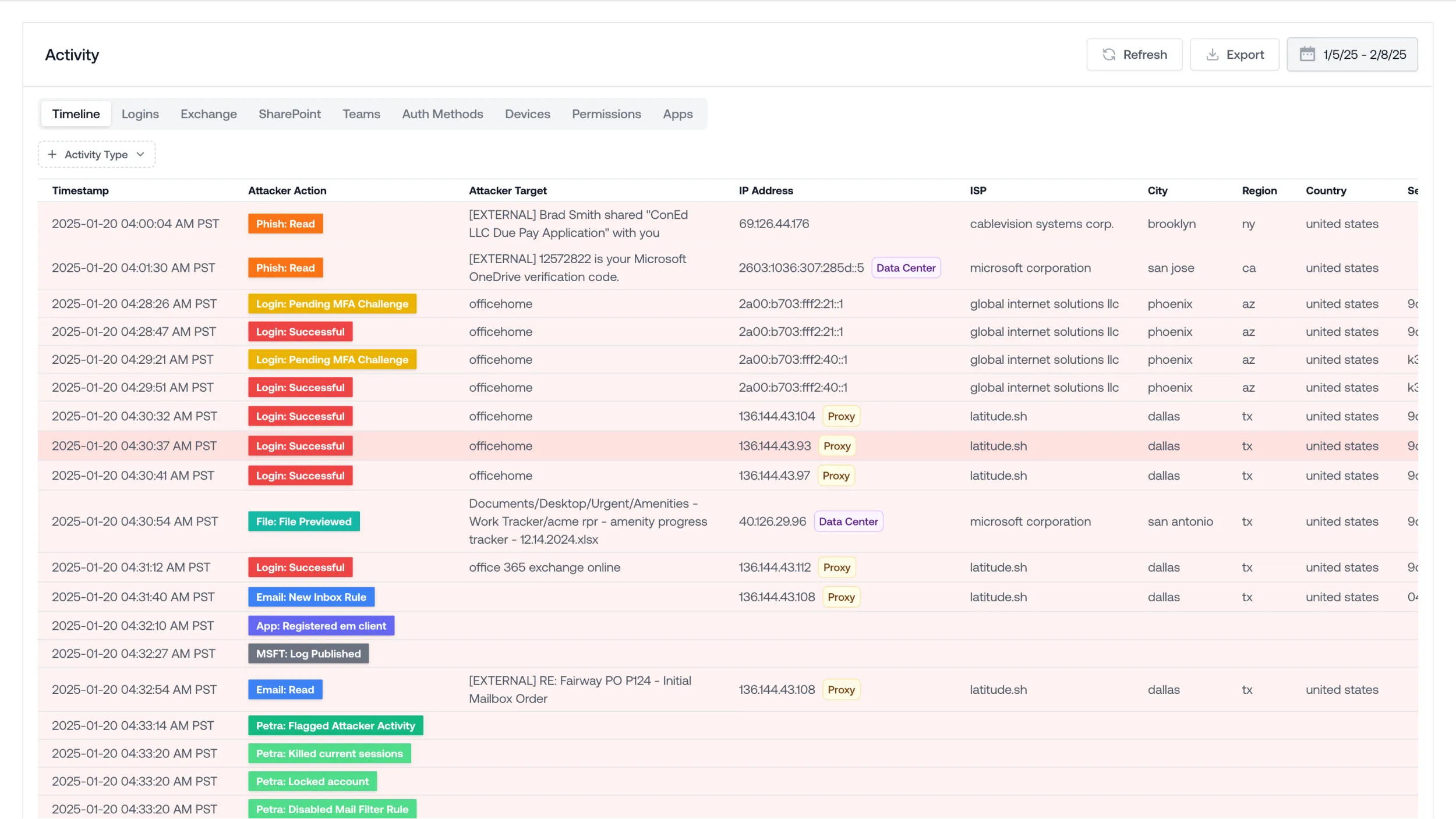
Detects on logins, inbox rules, app registrations, email reads, email sends, email deletions, file reads, file sends, file modifications, file deletions, teams messages sent, teams messages received, MFA methods added, permissions updated, users added.
Data Sources
Processes Microsoft Management API.
Processes Microsoft Management API, Message Trace API, Unified Audit Log, Graph API, and P1/P2-specific APIs. Uses fastest available logs for detection.
Lurking Attackers Detection
Does not detect currently lurking stealthy attackers.
Detects currently lurking stealthy attackers (if any attacker activity in last 6 months).
Forensic Analysis
No forensic analysis.
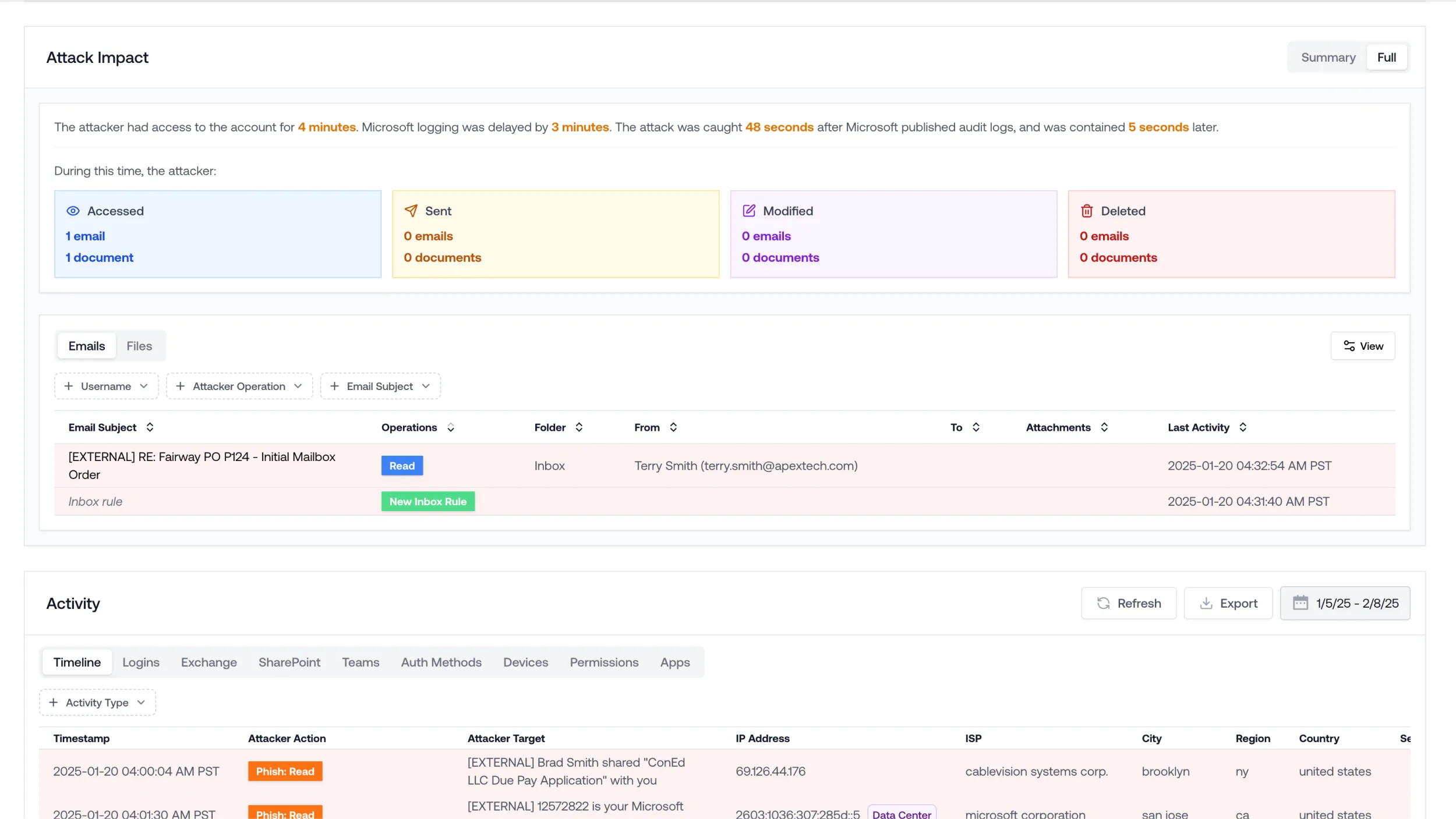
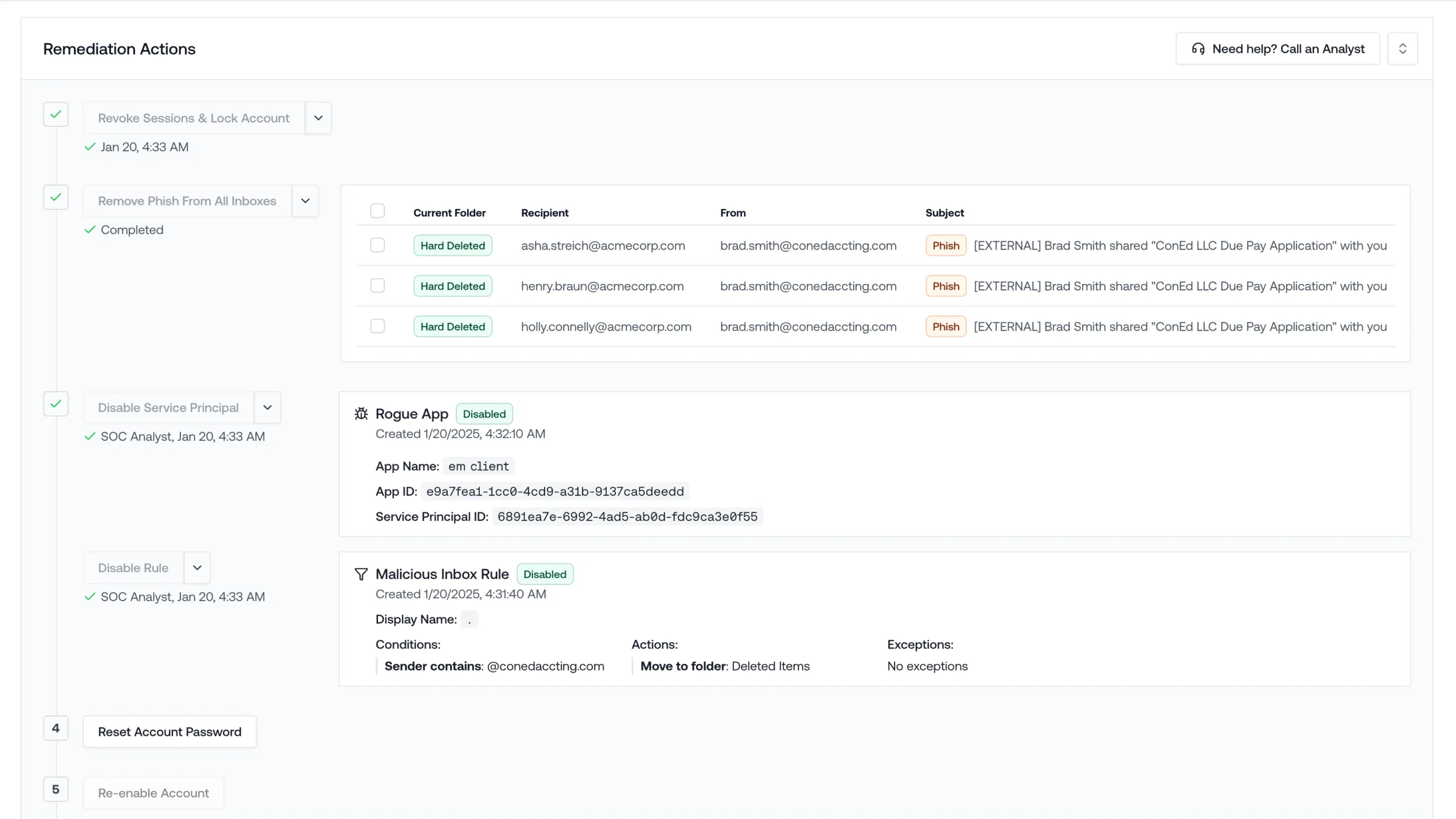
Offers forensic analysis (“Autopsy”), showing complete forensics for the past 6 months of compromises
EDR Product
Has an EDR product
Does not have an EDR product, focused on ITDR
SIEM Offering
Has a SIEM product
Only offers an M365 SIEM, included with ITDR
SAT Product
Has a SAT product
Does not offer SAT, focused on ITDR
Post-Incident Reporting
No client-ready PDF
Excel + PDF, client-ready
Post-Incident Reporting
N24/7 SOC, Human staffed and AI-assisted
24/7 SOC, Human staffed and AI-assisted (US-based).
Client-Ready Forensic Reports
No post-incident client-ready PDF.
Generates post-incident forensic excel and client-ready PDF.
Attack Timeline Visibility
Shows attack timeline for some incidents (emails/files accessed, emails sent, etc.)
Shows attack timeline, showing what the attacker touched (emails/files accessed, emails sent, persistence added, etc.)
Alert Tuning & False Positive Reduction
Tunes manually. Users whitelist/blacklist VPN use.
Tunes dynamically. Uses behavior (analyzing 50x logs) to cut down on proxy/VPN use alerts.
Geo-Based Alerting Model
Users maintain travel allowlists and geo-blocking, updating when users travel.
Users do not maintain travel allowlists. Dynamically tunes to reduce dependence on geo-based alerting.
Detection Speed
Response time varies, some caught very quickly (e.g. axios-based attacks), some caught days/weeks later (see case study)
Response time generally fast, ~1-3 mins after audit logs published (see large deployment stats).
Pre-Sales & Trial Model
Gives 30 days free for new tenants as pre-sales tool.
Gives 14-day trial period for MSP, then offers prospect pre-sales report showing past 6 months of compromises and their impact.
Anonymized Attack Timeline for Sales
No anonymized attack timeline
Generates an anonymized attack view and PDF for any incident (cautionary tales from without ITDR or fast-caught compromises with ITDR). Useful for sales.
Log Retention Requirements
Requires SIEM product for log retention
Retains logs for 1 year for free (M365 SIEM). Uses for behavioral baselines.
Log Search & Storage Duration
With SIEM, logs are searchable for 1 month and in cold storage for 12 months.
With included M365 SIEM, logs are stored and searchable for 12 months.
SOC Team Structure
Remote team.
In-person team.
MSP-Only Focus
Sells direct and to MSPs.
Sells to MSPs only.
Company Tenure
Been around for 10 years.
Been around for 2 years.
Platform Coverage
Offers Google Workspace protection (in beta testing)
M365-only. Google Workspace not yet supported.
Phishing Root Cause Identification
Does not identify phish email that caused the compromise.
Detects phish email that caused the compromise, retracts from other inboxes to prevent lateral attacker spread.
Frequently asked questions
You have questions? We have answers. We're here to help.
How long does an Autopsy take to finish?
Typically just 24 hours after initiated, analysis is finished and an Autopsy Report is ready to review.
Does an Autopsy process email contents?
No. An Autopsy just processes the metadata of your Exchange activity, not the contents.
We have email security. Would it still be helpful to run an Autopsy?
Yes. Most of today’s successful attacks bypass email security, often via trusted third-party phishing and U.S. IPs. Most Autopsies that find attackers occur on companies with email security.
Do I need an admin account to initiate an Autopsy?
Yes, but you don’t need to give us access. We can give you a link to kick off the Autopsy directly.

Try Autopsy for free
Autopsy produces BEC forensics in 24 hours, showing you everything the attacker did and producing a client-ready PDF report.